IT Security in 2016: What Comes Next?
The last several years in IT Security have been full of surprises as well as the fulfillment of predictions that have been made. If you recall back to 2014, the famed credit card breaches that took place were predicted by most and ultimately held true to form. We had a rash of major breaches, including Target, The Home Depot, Michael’s, and many others that took place, resulting in the theft of hundreds of millions of credit and debit cards.
In 2015, the prediction was that healthcare and subsequently medical records were going to be the next big focus for hackers and criminals. Unfortunately, that prediction held true and 2015 was epic, not in a good way, in terms of the number of possible healthcare records that were exposed due to a breach of some sort. In fact, after all is said and done, in 2015 was a year to forget for healthcare as the top 10 breaches of the year accounted for around 110 million individuals affected by these breaches. For those keeping score at home, this is roughly 1/3rd of the population of the United States, assuming that each record stolen was a unique individual.
Here we are barely into 2016 and the question remains, what will be the “next big thing”, target, or trend for IT Security for the coming 12 months? While I am sure that we all have some suggestions and opinions on this, let’s list out some of the possibilities, in no particular order:
- Healthcare – Ahhh Healthcare, you remain on the list for another year. If 2015 was such a successful year in terms of healthcare breaches, why would it be on the list for this year as well? That’s a great question and I’m glad that you asked! For healthcare it comes down to 3 of key items: Success, Availability, and Opportunity. Medical records are worth far more on the underground market than a credit card number. Combine that with the fact that Healthcare seems to be a bit behind in terms of IT Security being a priority for organizations and you have a perfect storm brewing
- The Internet of Things – This is a fancy term that gets kicked around frequently. I am not quite sure who invented it but they are a genius as it has certainly caught on. What this essentially means is that as we connect more and more “things” or devices to the Internet, the greater the risk around our information being stolen or compromised. From thermostats to cars to wearables, the more we connect to the Internet, the greater the need is to ensure that we are securing these items to prevent hackers from overtaking them
- Business Email Compromise (BEC) – This one fascinates me to be honest. For those who don’t know, this is where a hacker “spoofs” the email address of the CEO of a company and asks a finance person to make a wire transfer to a fake company, usually for a lot of money, that is shockingly located outside the United States which provides zero ability to retrieve the funds. On the surface you might ask how this is even remotely possible, but let me assure you that it is 100% possible. In fact, according to the FBI’s data as of August 27th, 2015, the total number of victims in the United States from October 2013 to August 2015 was 7,066 and accounted for $747,659,840.63. Let that sink in for a moment and then think about this: Those numbers don’t account for the final three months of 2015 which is when we started to hear more and more about this scam also referred to as “CEO Fraud”
- Phishing/Spear Phishing/Malware Campaigns – This is a lot of stuff to lump into one category and you could argue that each could be a separate bullet point which is true, but in the idea of keeping this shorter than a novel, I decided to combine them. Phishing and Spear Phishing campaigns are getting more and more sophisticated and are targeting more and more people. Combine this with the fact that this is a simple and effective way to spread malware and boom, there is that perfect storm again!
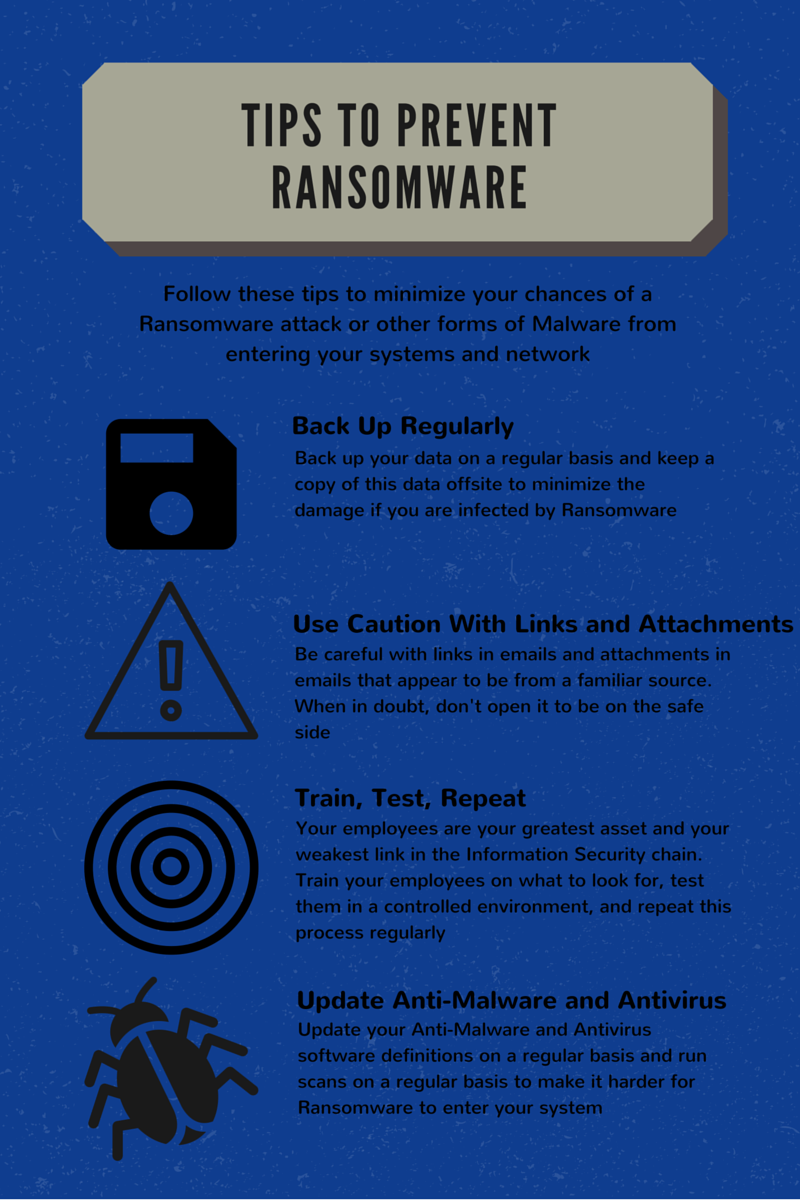
I really don’t want this blog post, my first of 2016, to be all doom and gloom. This is a season of starting fresh and making resolutions of what you hope to accomplish in 2016. With that, let me give you some suggestions on how to combat these IT Security nightmares from wreaking havoc on your organization:
- Conduct a thorough IT Risk Assessment – Never done one? Now’s the perfect time to start. You did one last year? Great! Start 2016 off right by updating the one from last year. Security is not a point in time event, it is ongoing and therefore your risk assessment process should be as well!
- Build a Culture of Security – What does that mean? IT Security has to be a top down philosophy that is taken serious by Sr. Management and employees are empowered to challenge questionable situations that they encounter. See some strange guy walking the hallways? Ask him what he’s up to. Did your CEO supposedly just ask you to wire $850,000 to some company in Zimbabwe that you have never done business with? Pick up the phone and give them a call to confirm. Did your IT Department just call you from an outside number and ask you to install some crazy software onto your computer? Ask them where they are located and why they aren’t calling from an inside number. You get the point, right?
- Test, Test, Test – Policies and Procedures are awesome and they are necessary. Even better is training your staff on those policies and procedures. But what happens when the rubber hits the road and they get a suspicious email with a shipping invoice? What do they do then? Test your employees and let them put their knowledge to work in a controlled environment as opposed to the criminal enterprise that is trying to take down your organization
The first blog post of 2016 is in the books! We here at Compass want to assist you however we can to make sure that your 2016 starts off and continues down the right path. Feel free to reach out to us, we’d love to hear from you!
Contact Us
Share this
You May Also Like
These Related Stories

Social Engineering - What You Need to Know

Social Engineering - Mitigating Your Risk
.webp?width=2169&height=526&name=Compass%20white%20blue%20transparent%202%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)
No Comments Yet
Let us know what you think