
Welcome to Cybersecurity Awareness Month!
As you know, every October is Cybersecurity Awareness Month. For me, every month here at Compass is Cybersecurity Awareness Month as we spend a significant amount of time educating and empowering our customers and prospects on how to mitigate their risk. This is why we have made a strong commitment to our monthly webinar series and why, for October, we will be presenting weekly webinars focused on Information Security.
The name of the game in Information Security is to mitigate your risk. We throw that phrase around all the time, but what does it mean? If we turn to our trusted dictionary, the word mitigate means, "to make something less severe, harmful, or painful." So to mitigate risk means to make the risks associated with information security less severe, harmful, or painful. Notice that I did not say we were going to eliminate Infosec risks. Why? Because that is not realistic. There is no true way to completely eliminate risks in anything, especially information security. So what can we do to mitigate our risks around Information Security? Well, without giving away all the information that will be in our October 6th webinar, here are the three main buckets that we look at when helping an organization mitigate their risk:
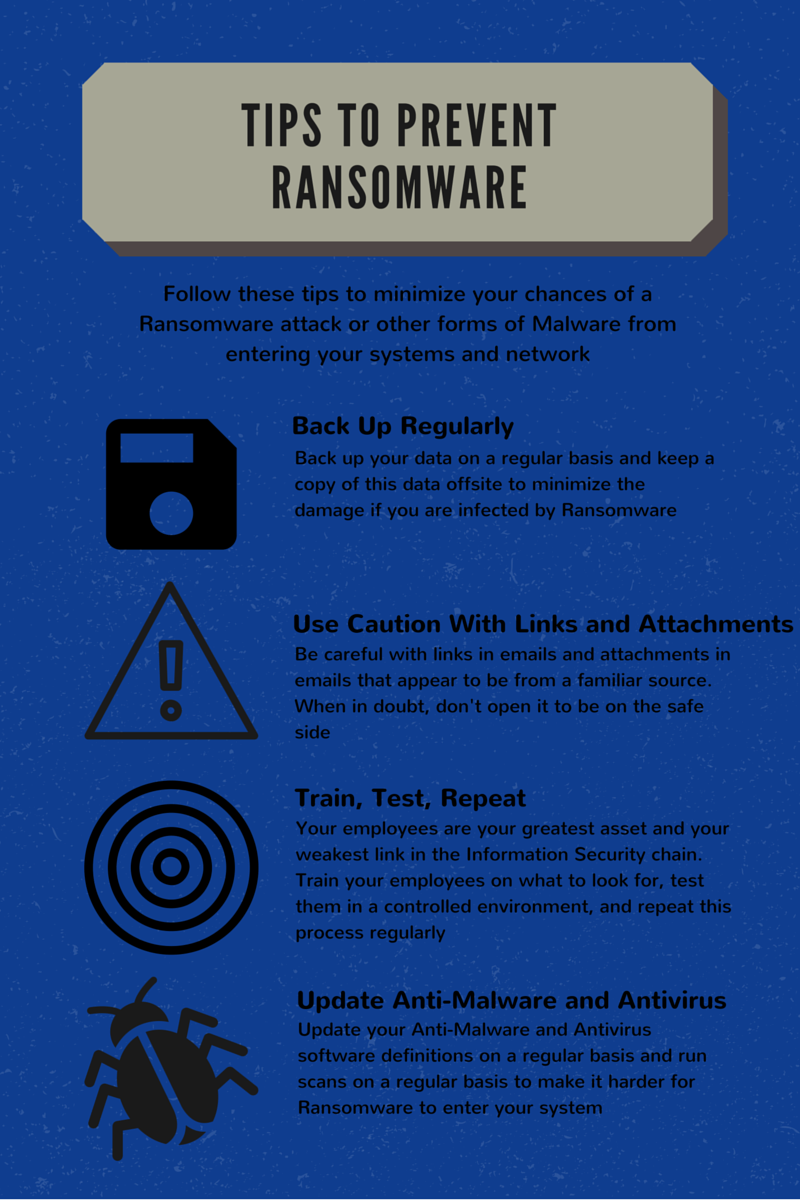
- People - This is a large part of Information Security. No matter what technology you have in place, there is a person that handles managing that technology. Also, there are end-users of technology that pose a risk, through no real fault of their own. Whether clicking on a link that installs malware or letting a "remote tech support rep" take control of your system to "install programs", I am confident most users do not purposely do these things to cause harm. This is why we suggest Security Awareness Training Programs (hint: programs, not once a year training), Policies and Procedures, and Social Engineering Assessments to "test" your employees.
- Process - The organizations that we work with handle some form of sensitive information. Whether it is credit card information, protected health information, or the personally identifiable information of their employees, every company has some responsibility around protecting that information. So we look at the process of how your organization receives that information, transmits that information inside your network, and how that information leaves your company to its next place. Therefore, we look at things like access control to determine who needs to have access to what information and why. We look at things like least privilege and the use of administrator accounts on local machines. All these processes (or lack there of) have an impact on the risk associated with the information that your company possesses.
- Technology - Technology gets all the glory, and for good reason. We have come a long, long way in terms of technological advances which is a positive thing. Yet, with great reward comes great risk. As fast as we can stand technology up, are we able to provision the security around that technology as quickly? Are we segmenting networks that process sensitive information (PCI Compliance anyone?) What software platforms process and transmit sensitive information? These are all questions around the use of technology and while technology remains the lifeline of many organizations, the improper security of technology can have lasting, negative impacts.
Now the question becomes, with all these moving parts, what can we do to mitigate our risk? On Thursday, October 6th, Compass will be hosting an educational webinar titled "The Top 5 Tips to Mitigate Your Risk." This will give you 5 "quick-hits" that you can put in place that will mitigate your risks of a data breach/loss. Details are below and click on the button to register. We look forward to seeing you on the 6th!
What: Top 5 Tips to Mitigate Your Risk Webinar
When: Thursday October 6, 2016 @ 1:00 PM EST
Where: Online, register below



No Comments Yet
Let us know what you think