Share this
Previous story
← Ransomware - The Imminent Threat to Your Data
Through my work at Compass IT Compliance I was recently contacted to deal with an issue regarding a Mac computer acting suspiciously. What does suspicious mean? In the case of this particular Mac, whenever a user tried to open the Safari web browser they were getting directed to the highly unusual page weknow.ac. So, what is weknow.ac? I certainly didn’t know.
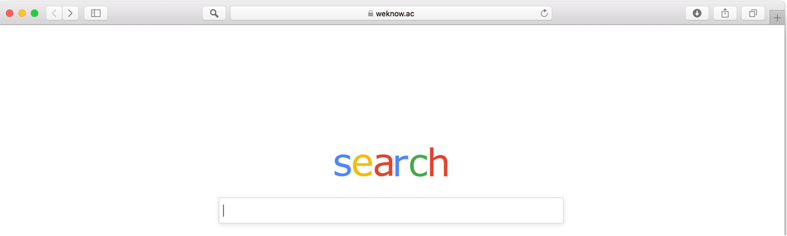
My first reaction was to open settings and see if I could set the home page back to a blank page. To my surprise, any adjustment I attempted on the home page setting failed.
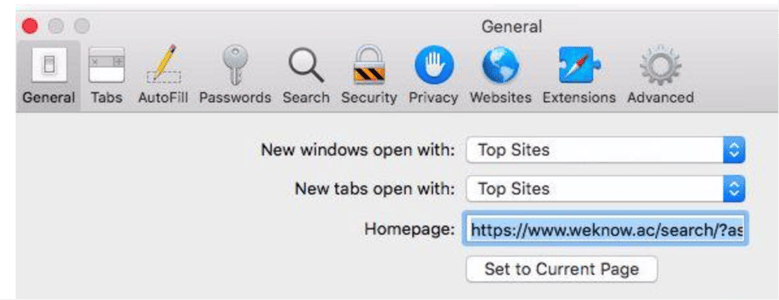
As soon as I observed this behavior, I immediately knew that I was dealing with a browser hijacker. A browser hijacker is defined as a “form of unwanted software that modifies a web browser’s settings without the user’s permission”. The result is the placement of unwanted advertising into the browser, and possibly the replacement of an existing home page or search page with the hijacker page. This type of malicious software is not only a nuisance, but it can be dangerous as it can redirect you to fake web pages that steal credentials. I remember first dealing with browser hijackers in the early 2000’s on Windows PCs, but this was a Mac and these types of things aren’t supposed to happen on a Mac (according to Mac fans and Apple). So, old becomes new again as we see often in technology.
It is true that the Mac OS (Operating System) is less prone to getting viruses and other malicious software. There are very specific reasons for this. Mac OS holds only 9.71% of operating system market share compared to Windows 87.48%. Less user base means that there are less bad actors writing code for the Mac OS. Another reason is the way that the Mac OS is built. The Mac OS is based off another operating system called BSD. BSD is referred to as a monolithic operating system which structures its file systems and control in a file-based way. Windows, on the other hand, relies on something called a registry. The registry in Windows is often a breeding ground and hiding place for viruses. These are two of the main reasons why Mac is less prone to getting viruses.
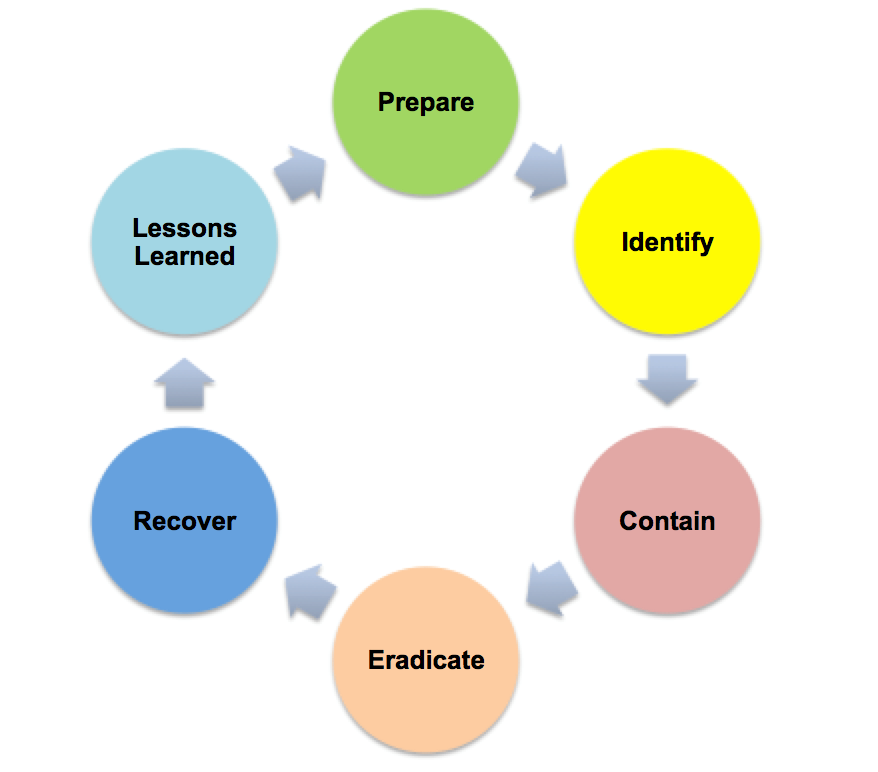
So, back to the issue at hand. In this case, the Mac definitely has some malicious software on it. Now we must remove it. The malicious software, just like any other malicious software, was hiding in the OS. We need to hunt it down and find it. Luckily, because of the nature of the Mac OS, we’re able to locate the malicious software much easier. There are multiple write-ups on the removal of this malicious software, so I won’t bore you with those details, but ultimately the software was removed and the machine was back to normal. This brings us to our last step, making sure that no credentials were stolen. This is key because of the nature of the attack. One of the things we did was to make sure that the user's particular services they use were not being logged into from locations not known to the end-user. Luckily, in this case, everything appeared normal and we were confident that no further compromise was achieved.
Macs certainly have their fair share of viruses out in the wild. In order to protect yourself, you want to make sure that you have antivirus software installed. If you are an IT director that manages a Mac infrastructure you will want to see about getting a centrally managed solution. If you suspect that you have a virus, take steps to remove the virus and then check to see if any further data breaches occurred as a result. Also, educate your users and make sure that AUP (acceptable use policy) is in place. The Weknow virus in the example above is a direct result of users using a work machine for purposes other than work.
These Related Stories


No Comments Yet
Let us know what you think