If you have been reading the blog for a while, you know that I take phishing examples that I receive or my co-workers receive, post them to the blog, and point out the things that you need to be careful of. I do this primarily to educate folks about what the latest threats look like, what differentiates a good phishing email from a bad phishing email, and also because it is fun (okay, I may be a little weird)! Well today is your lucky day because guess what? I got another phishing email over last weekend!
Before we dig into the nuts and bolts of this email, one thing that I want to point out is that this came to my work email address, not my personal email address. Second, this email ended up in my inbox and therefore made it through any spam and spoofing filters, which is moderately concerning. Third, if I were to categorize this phishing email, I would put it in the category of “Meh.” Not terrible, not great, just “meh.” Onto the actual email:
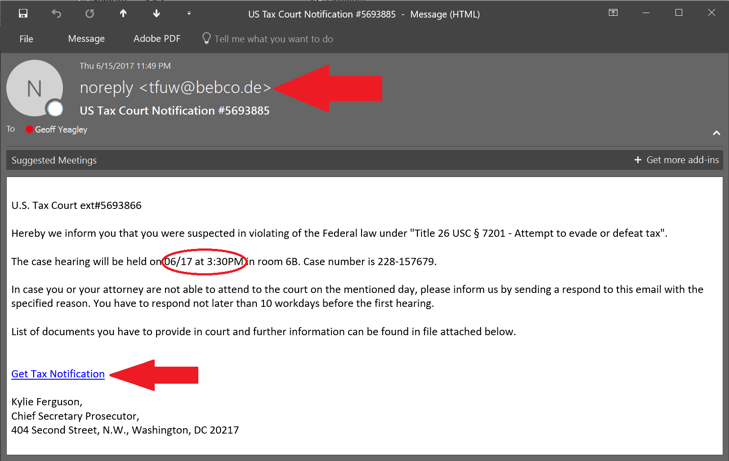
- The first red arrow points to the email address that the supposedly legit email came from. As you can see, it is from an email address that is based in Germany. The first question that should come to mind is why is someone from Germany emailing me to let me know that I have evaded taxes here in the United States? Red flag # 1. The next question should be why would the IRS email me to let me know I must be in court in 2 days (more on that later) at 11:49 PM at night? Red flag # 2
- See the date that is circled in red of 6/17/17 at 3:30 PM? Yeah, the 17th was a Saturday and I am fairly certain that no courthouses are open on Saturdays. Secondly, I wouldn’t be able to attend anyway because I made plans to watch the U.S. Open. If you read a bit further down in the email, you see it says that if I cannot attend, either I or my attorney must notify them in writing no later than 10 working days before the first hearing. I am no math major, but my “notice” came only 2 days before the hearing, thus I am already in violation.
- The body of the email isn’t terrible. It isn’t great, but it’s not terrible. It is fairly well written, with the exceptions of choosing poor dates and making deadlines that have already passed, it really isn’t bad and the wrong person could easily see this as legit, at least on the surface.
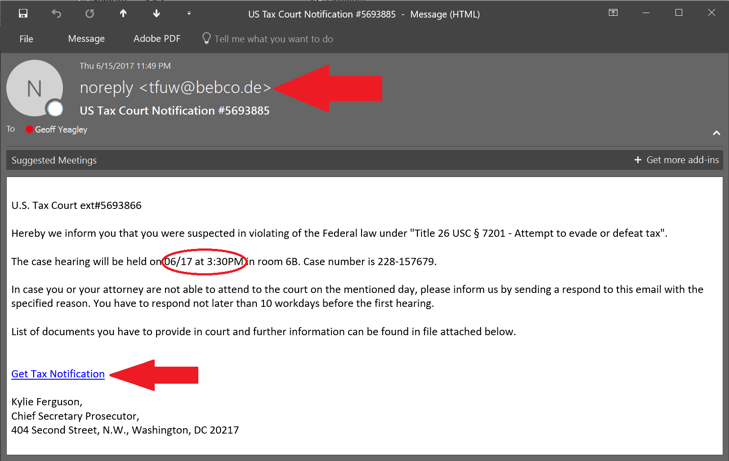
- The last red arrow points to a hyperlink where you can “Get Tax Notification.” This is where the danger lurks because once you click on that link, who knows what is going to happen? You might get infected with Ransomware or some other form of malware that does any number of things to your computer, none of which would be viewed as good. In fact, when I hover my mouse over the link, it shows me a link in Google Docs. Again, I am not the smartest duck in the pond but I am fairly certain that the IRS doesn’t use Google Docs to house their tax notifications or a “list of documents that I would need to provide in court.” I may be wrong but I doubt it!
Why did I take the time to write this blog post, besides the opportunity to poke some fun at a hacker trying to steal my information or infect me with malware? The answer is to educate you on what these threats look like. The threat landscape changes almost daily so the more information we can share with each other, the safer we will all become. Contact us if you want to learn more on how hacking has changed to expose the human element of information security.
Till next time, stay safe out there folks!

No Comments Yet
Let us know what you think