How Human Error Causes Cybersecurity Breaches
by Jake Dwares on February 4, 2026 at 4:22 PM
Most organizations invest in firewalls, encryption, and sophisticated security tools. Yet despite these technological defenses, humans remain the weakest link in the cybersecurity chain. A single misplaced click, a reused password, or a moment of distraction can unravel even the most …
What Is the Best Way to Train Employees on Cybersecurity Awareness?
by Patrick Laverty on October 29, 2025 at 1:00 PM
In today’s connected world, cybersecurity is not just the responsibility of the IT department. Every employee plays a role in protecting company data and systems from threats. With human error contributing to the majority of security incidents, organizations that invest in effective c …
What Are the Best Ways to Prevent Social Engineering Attacks?
by Patrick Laverty on August 20, 2025 at 1:41 PM
When I give speeches or training sessions on social engineering, I always start with a simple mantra: V & V—Verification and Validation. It's not flashy, but it's foundational. My bet is that if you verify and validate everything, no social engineering (SE) attack can succeed. I'v …
Why Is Social Engineering a Threat to Businesses?
by Jesse Roberts on August 7, 2025 at 11:00 AM
When most people think of cybersecurity threats, they picture viruses, ransomware, or brute-force attacks hammering away at firewalls. But some of the most effective attacks don’t need advanced code or malware. They just need a willing person to pick up the phone, click a link, or tru …
Unpaid Toll Text Scam? Cybersecurity Experts Explain Signs
by Nicholas Foisy on March 3, 2025 at 1:57 PM
Receiving a text about an unpaid toll can be alarming. With so many people using toll roads daily, a message demanding payment might seem legitimate at first glance. However, cybersecurity experts warn that many of these texts are scams designed to steal your personal and financial in …
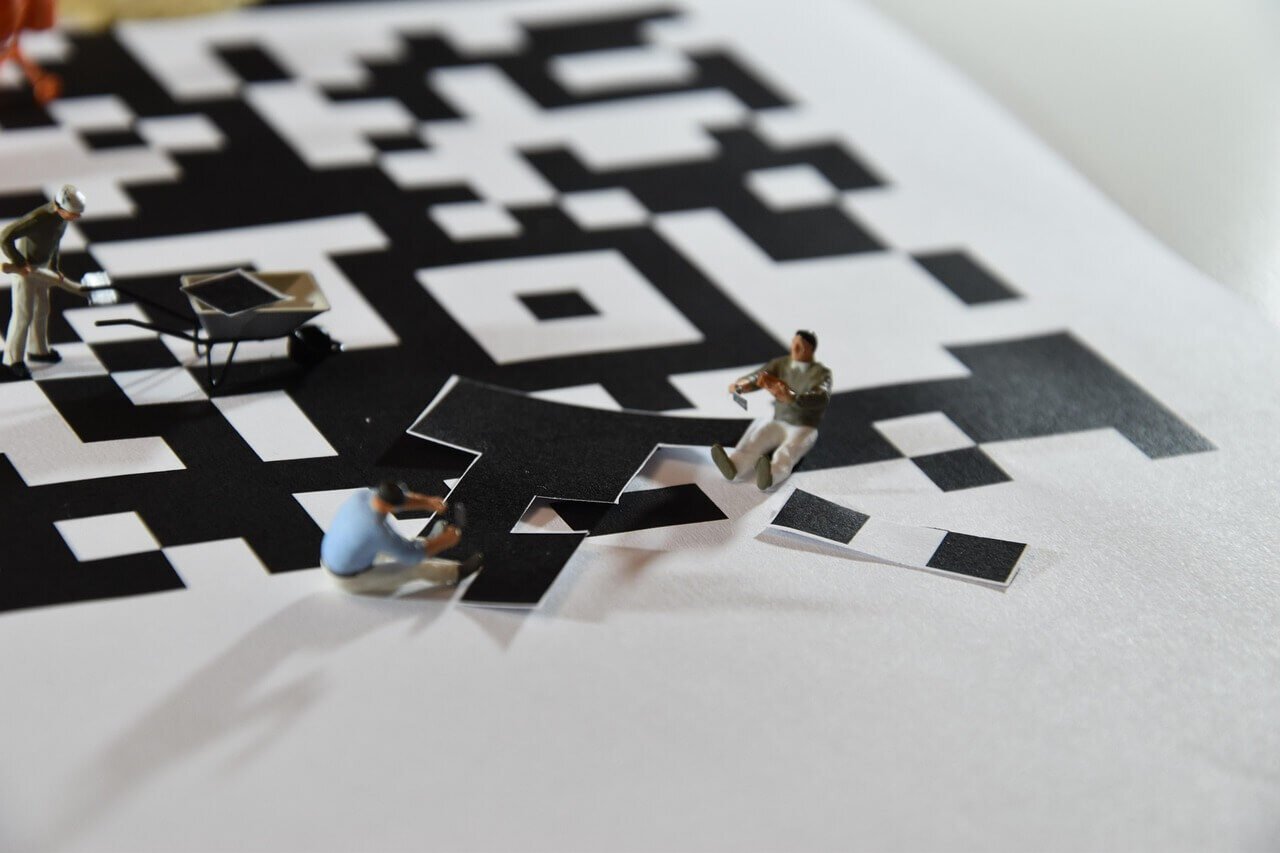
QR Code Package Scam: What It Is & How to Spot It
by Nicholas Foisy on February 14, 2025 at 1:14 PM
In recent months, reports of a new scam involving unexpected packages and QR codes have emerged, raising concerns among consumers and cybersecurity experts alike. This scam, which appears to be an evolution of the well-known "brushing" scheme, is designed to trick recipients into scan …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)