The SOC 3 Report: Your Most Underutilized Trust Asset
by Jerry Hughes on April 24, 2026 at 2:03 PM
In today's marketplace, trust is currency. Prospects evaluate vendors with increasing scrutiny, procurement teams demand proof of security controls before signing contracts, and buyers at every level want assurance that the organizations handling their data take that responsibility se …
Your GRC Tool Has Limits: Why a CPA Must Be Behind Your SOC Report
by Jerry Hughes on April 9, 2026 at 12:30 PM
There is a quiet misconception circulating in the compliance space, and it is worth addressing directly. As GRC automation platforms have grown in popularity, and as their marketing has increasingly emphasized “SOC 2 readiness,” “continuous compliance,” and “audit preparation” some or …
Security Awareness Training for SOC 2: What Your Auditor Expects
by Janelle Lewis on March 26, 2026 at 4:41 PM
On March 15, 2026, the Chittenden Solid Waste District of Vermont lost $3 million to a single phishing attack. That was not a rounding error in someone’s budget; it was a significant portion of the district’s annual funding, gone in the span of a few fraudulent emails.
SOC 2 Remediation Roadmap: Turn Exceptions Into Progress
by Rachel Hughes on January 30, 2026 at 11:52 AM
Your SOC 2 audit report just landed on your desk, and you've spotted exceptions. Before the panic sets in, take a breath. Finding exceptions in your SOC 2 audit doesn't signal impending disaster or business failure. In fact, exceptions happen even to well-managed, security-conscious o …
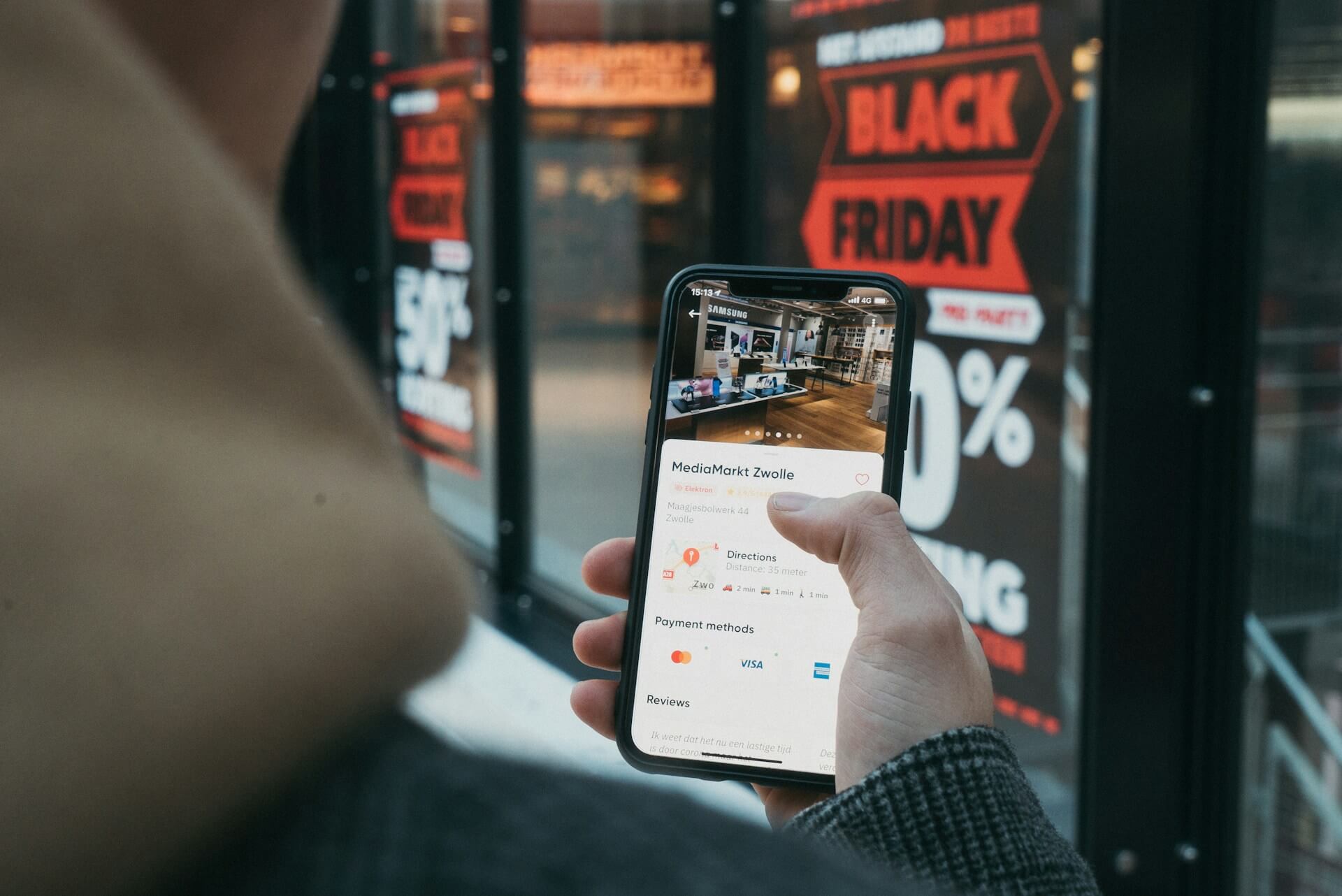
Why Holiday Peak Readiness Depends on Strong SOC 2 Compliance
by Jerry Hughes on November 26, 2025 at 12:00 PM
Black Friday is no longer a single day of crowded stores and doorbuster sales. It has become a long digital stretch that can determine the financial outcome of an entire year for many retailers. For some online merchants, the holiday shopping season represents up to a third of their a …
SOC 2 & ISO 27001 Together: How to Build One Unified Plan
by Derek Boczenowski on September 25, 2025 at 1:00 PM
For growing organizations, SOC 2 and ISO 27001 are no longer optional — they’ve become baseline expectations from customers, partners, and regulators. Both frameworks help you prove that you are serious about protecting sensitive data, but pursuing them separately can feel like runnin …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)