Third Party Administrator (TPA) Risks: IT Security & Compliance Guide
by Kyle Daun on May 27, 2026 at 4:05 PM
If your organization handles sensitive data and outsources any operational work, there is a good chance a Third Party Administrator (TPA) is somewhere in your environment. Maybe they process claims for your self-funded health plan. Maybe they handle 401(k) recordkeeping. Maybe they ar …
When Vendors Get Hacked: Your Guide to Third-Party Data Breaches
by Derek Boczenowski on December 3, 2025 at 3:03 PM
In today's interconnected business ecosystem, organizations rely heavily on third-party vendors for everything from payroll and marketing to cloud hosting, customer support, and specialized financial-services processing. While these partnerships unlock efficiency and innovation, they …
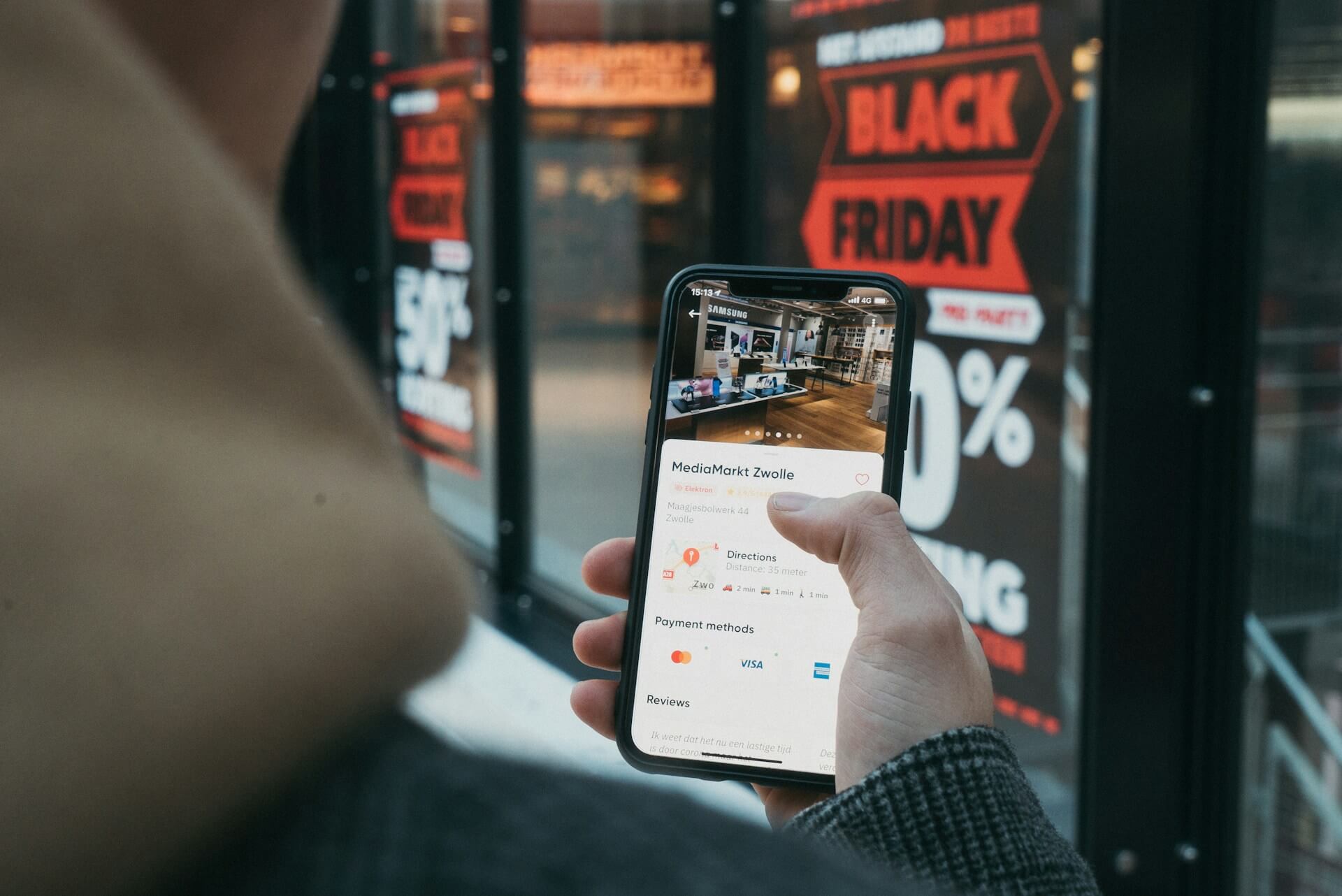
Why Holiday Peak Readiness Depends on Strong SOC 2 Compliance
by Jerry Hughes on November 26, 2025 at 12:00 PM
Black Friday is no longer a single day of crowded stores and doorbuster sales. It has become a long digital stretch that can determine the financial outcome of an entire year for many retailers. For some online merchants, the holiday shopping season represents up to a third of their a …
Managing Vendor Risk Without a Dedicated Team
by Donald Mills on September 23, 2025 at 2:00 PM
High-profile breaches have shown that attackers often take the path of least resistance—and that path is frequently through a third party. The 2013 Target breach is the textbook example: attackers used a compromised HVAC vendor to access Target’s network, leading to a massive payment …
Security Questionnaires: How to Streamline Responses & Save Time
by Alexander Magid on September 2, 2025 at 1:46 PM
As vCISOs serving organizations across the country, we spend a significant amount of time on both sides of the security questionnaire process. We respond to them on behalf of our clients, and we also issue them as part of vendor risk management programs. The reality is the same in eit …
Your SOC 2 Audit Is Complete – What Comes Next?
by Jerry Hughes on May 28, 2025 at 4:03 PM
Congratulations on achieving SOC 2 compliance! At Compass, we understand the effort it takes to meet the rigorous Trust Services Criteria and successfully navigate the audit process. Securing your SOC 2 attestation is a significant milestone, demonstrating your organization’s commitme …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)
%20Risks%20IT%20Security%20%26%20Compliance%20Guide.jpg)
.jpg)