Share this
Previous story
← Moving From SSAE 16 to SSAE 18....
Ransomware has dominated the news recently when it comes to IT Security. In fact, it was recently reported that 1 out of 5 companies that suffers a Ransomware attack ends up going out of business at least temporarily and 30% of affected companies lost revenue. Now we turn to the question of how does Ransomware get into a company? While everyone has heard of Phishing and read blog posts on what is phishing, I want to focus on the different types of phishing and ultimately what the goals of phishing are.
Before we get into the different types of phishing emails associated with Ransomware and Malware, we need to identify the goal of these activities. The ultimate goal is to make money. Whether that is to get you to pay a ransom or to steal sensitive information (credit card numbers, social security numbers, etc.) that will later be sold, the goal is to make money. This is a business that criminal organizations engage in that has become very profitable. And the key to these activities is email phishing campaigns designed to take advantage of the weakest link in IT Security: People. Here are three different types of phishing emails that target your employees with the goal of making money:

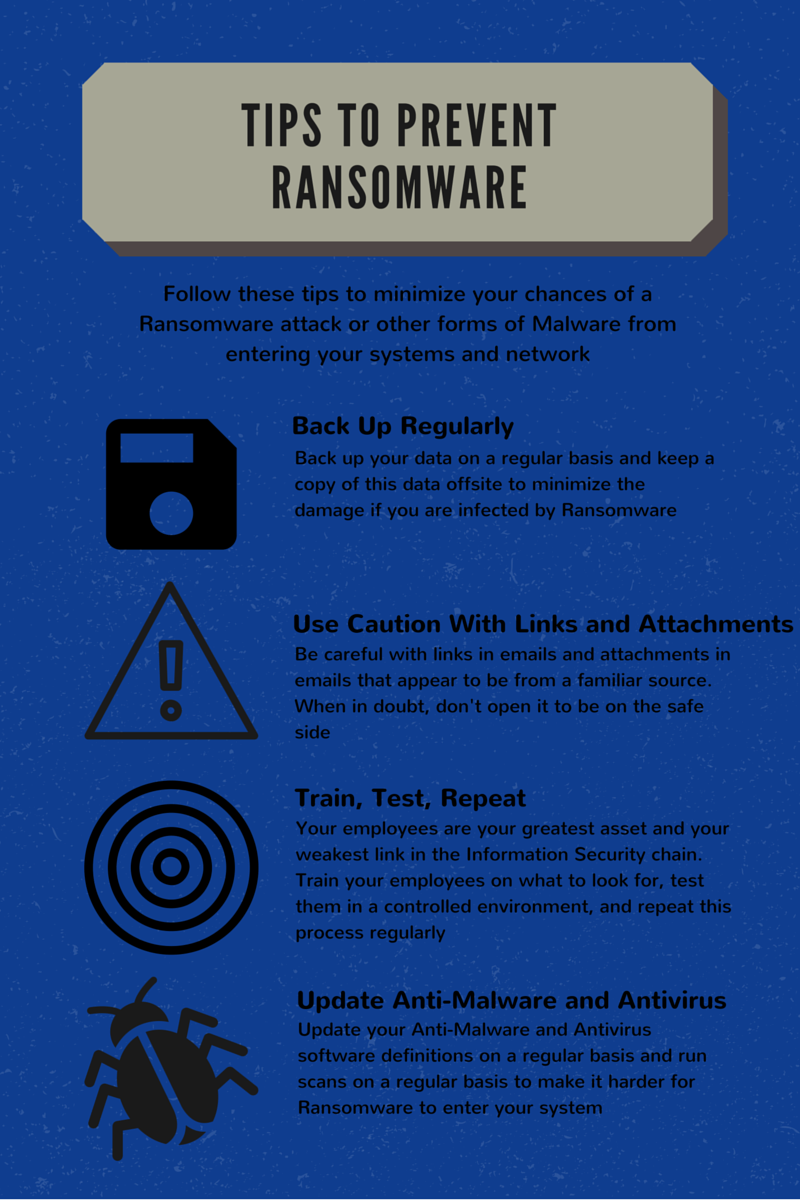
There are many more types of phishing campaigns out there, these are just 3 different examples of the tactics that these criminal entities use to steal your information or data and make money. So the next question becomes, how can I protect myself from this type of scenario? The short and simple answer is to ensure that your staff is properly trained. As we all know, it is far more detailed than that.
These Related Stories
.jpg)
No Comments Yet
Let us know what you think