Share this
Next story
Ransomware Alert: New Strain in the Wild →
Friends of Compass,
On this blog, phishing examples are nothing new. But, it is our job to share this information with you so that you stay alert, know what the threats are, and what you can do in the event you fall victim to an attack.
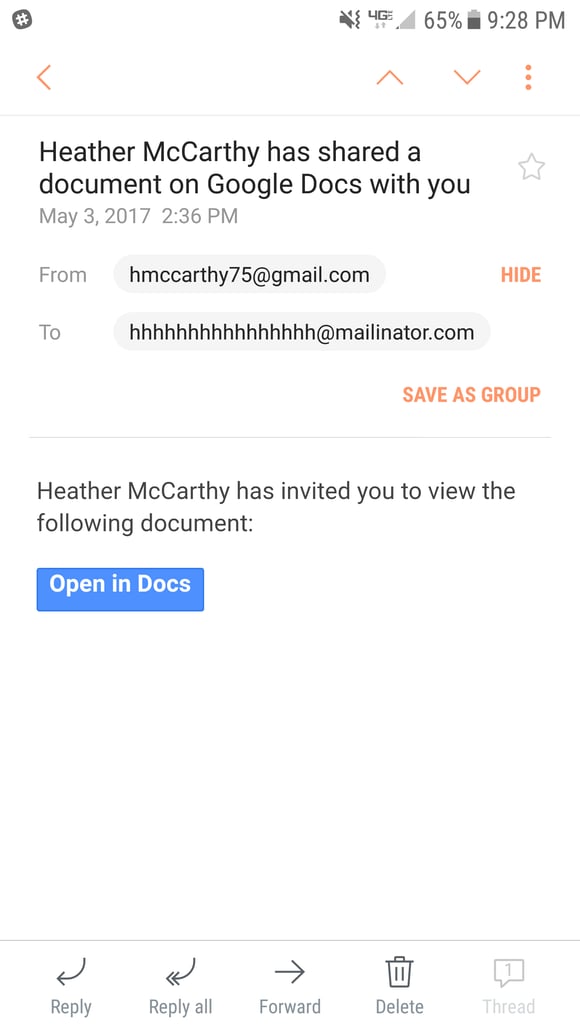
You may have seen the recent reports of a Phishing scam involving Google docs currently making it’s rounds. To ensure your safety and spread awareness we’ve provided a brief outline for you and your staff detailing what to be on the lookout for and what should do in the event you’ve already clicked the bait.
What to watch out for (See image below):
What to do if you’ve clicked the link:
The moral of the story is don't click the link. However, this is easier said than done, especially when the email looks legit and might even come from someone you know. If you get an email and it seems suspicious, confirm with the sender (if you know them) that they in fact sent you the email. If they didn't, that is a HUGE red flag and don't click the link! If it is from someone you don't know, just don't click the link. Resist the temptation as the only thing that you are missing out on is a bunch of trouble!
These Related Stories


No Comments Yet
Let us know what you think