Share this
Previous story
← SSAE 18 SOC Reports: The 5 Trust Services Criteria
Spear phishing is a deadly form of targeted social engineering. The main difference between spear phishing and traditional phishing is that spear phishing targets a certain user or users by using important facets of their life against them, while traditional phishing targets a broad group of people. One way to visualize spear phishing would be exactly how it sounds, using a spear to lock in and target a specific fish with precision, while traditional phishing is casting out a wide net in the ocean to see what you can catch. In my previous blog post, I discuss how attackers will look you up on social media to find out personal details about you and craft an attack that won’t make you think twice. In this blog I’m going to show you how to spot a spear phishing attack to better prepare you for these situations.
Below is an example of what a spear phishing email might look like. For context, this girl named Kathryn is going to college ABC and has monthly loans to pay off while she’s at school. The attacker has found out what school she goes to by browsing her social media profiles and used that information to craft up a phishing email very specific to her, which is intended to mimic a student loan payment notification from Kathryn’s school.
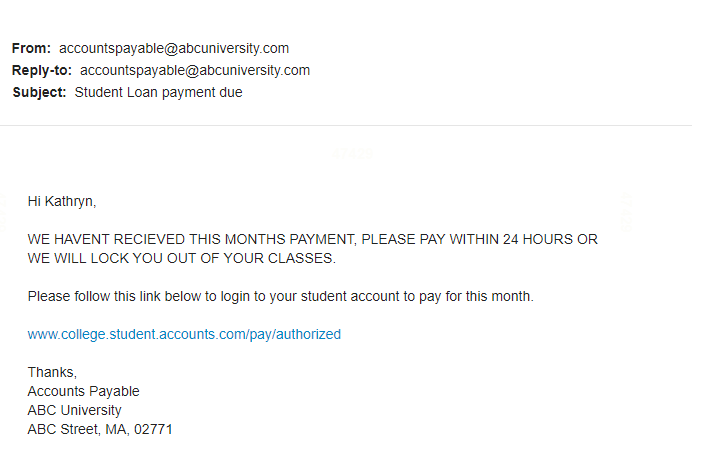
There are several red flags that will help you identify if you are being targeted by spear phishing. Always make sure to thoroughly read the email to check for spelling mistakes as well as the sender’s email address to see if it would match up or if the names are spelled correctly. In this case, Kathryn should hover over the payment link in the email to see if it directs her to the legitimate university site. If she is still unsure, she can check to see if her bill truly is outstanding by visiting the school’s official site, going into the financial aid office, or calling them. If you are suspicious, never click the link in the email!
Here’s another example of a spear phishing attack below. John Doe, an employee of XYZ company received this email from an individual claiming to be his manager. In this case, the attacker went on LinkedIn to find out that John Doe works for company XYZ and that his title is Sales Representative. From there, the attacker then looked up all employees from company XYZ on LinkedIn and found out that Susan Smith is the Sales Manager. According to the email John received his manager Susan is urgently asking him to get three $100 Amazon gift cards to her ASAP, and that she can’t answer her phone due to a meeting. The email goes on to threaten John with disciplinary action should he not comply immediately.
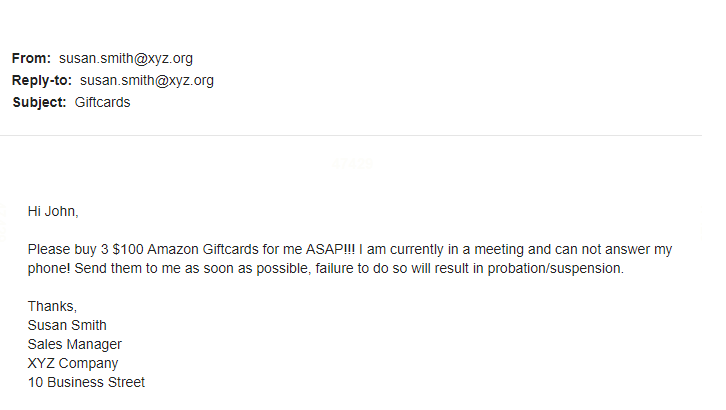
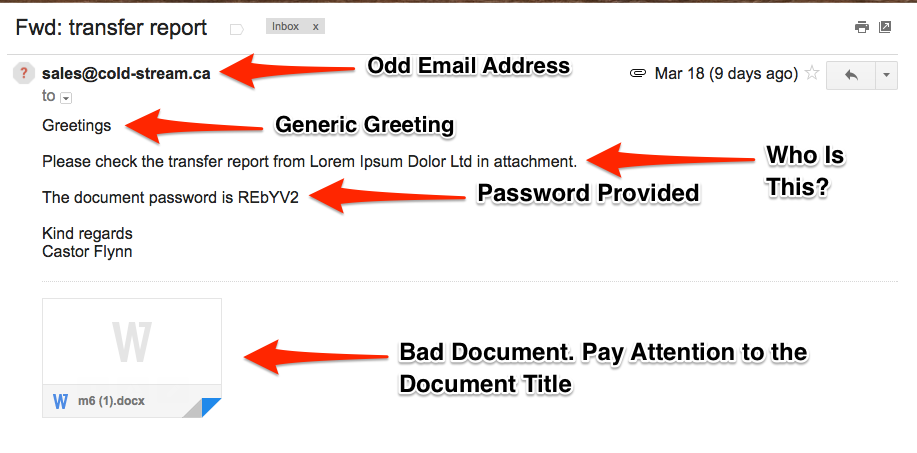
If John had gone ahead and complied, the attacker would likely ask him to send an email reply with the gift card numbers. This reply would be going to a fraudulent email address, and not to Susan. These types of spear phishing emails are very common in the business world. Don’t ever be afraid to call or message the individual that the email is claiming to have come from to see if they sent it. Although it’s important to always thoroughly check the spelling & grammar, sender email address, and links found in the email, spear phishing attacks will go the extra mile to disguise themselves. In some rare cases, it’s even possible to spoof the exact email address of the individual being impersonated, which would result in a phishing email showing the sender email address as completely correct with no spelling errors.
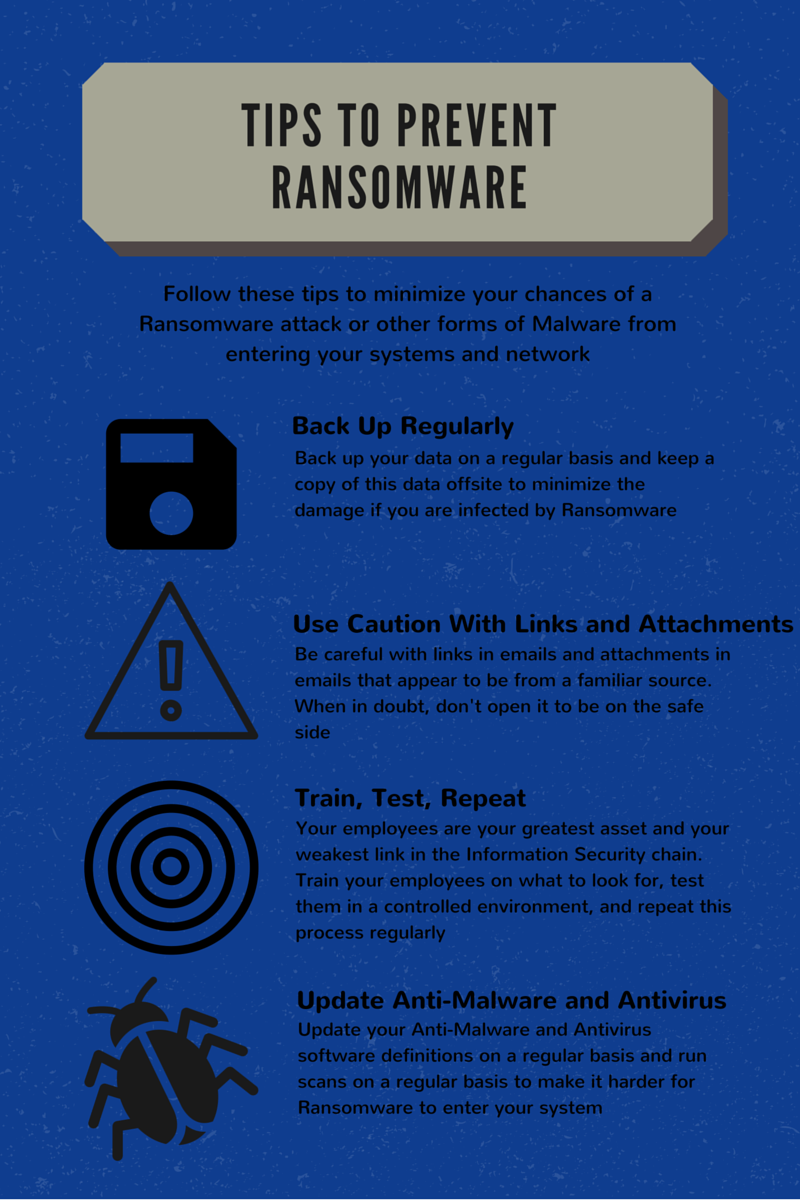
Attacks like those in the previous two examples attempt to play upon fear and urgency to get you to comply. These types of emotion tactics should immediately draw red flags. Spear phishing attacks have a higher success rate than traditional phishing due to the extra time and effort put in on research and crafting a very valid looking email. Do you think your employees are prepared to recognize spear phishing attacks? Compass IT Compliance has been carrying out spear phishing simulations for employers for nearly a decade. Using a list of employee emails and information, we can craft up targeted spear phishing emails to see whether your employees know how to react. We can also provide online security awareness & phishing training courses before and after these engagements. Contact us today to learn more!
These Related Stories

No Comments Yet
Let us know what you think