SAS 145 and IT General Controls: What Organizations Need to Know
by Bernard Gallagher on January 13, 2025 at 2:30 PM
The release of SAS 145 (Statement on Auditing Standards No. 145) represents a significant shift in how auditors evaluate and respond to the risks of material misstatements, particularly in complex IT environments. As IT General Controls (ITGCs) underpin key financial processes and rep …
Leveraging a Virtual CISO (vCISO) for SOC 2 Compliance
by Jeffrey Torrance on January 10, 2025 at 1:00 PM
In the rapidly evolving landscape of cybersecurity and data privacy, achieving and maintaining compliance with industry standards like SOC 2 is critical for businesses of all sizes. However, this process can be daunting, especially for organizations lacking the internal expertise or r …
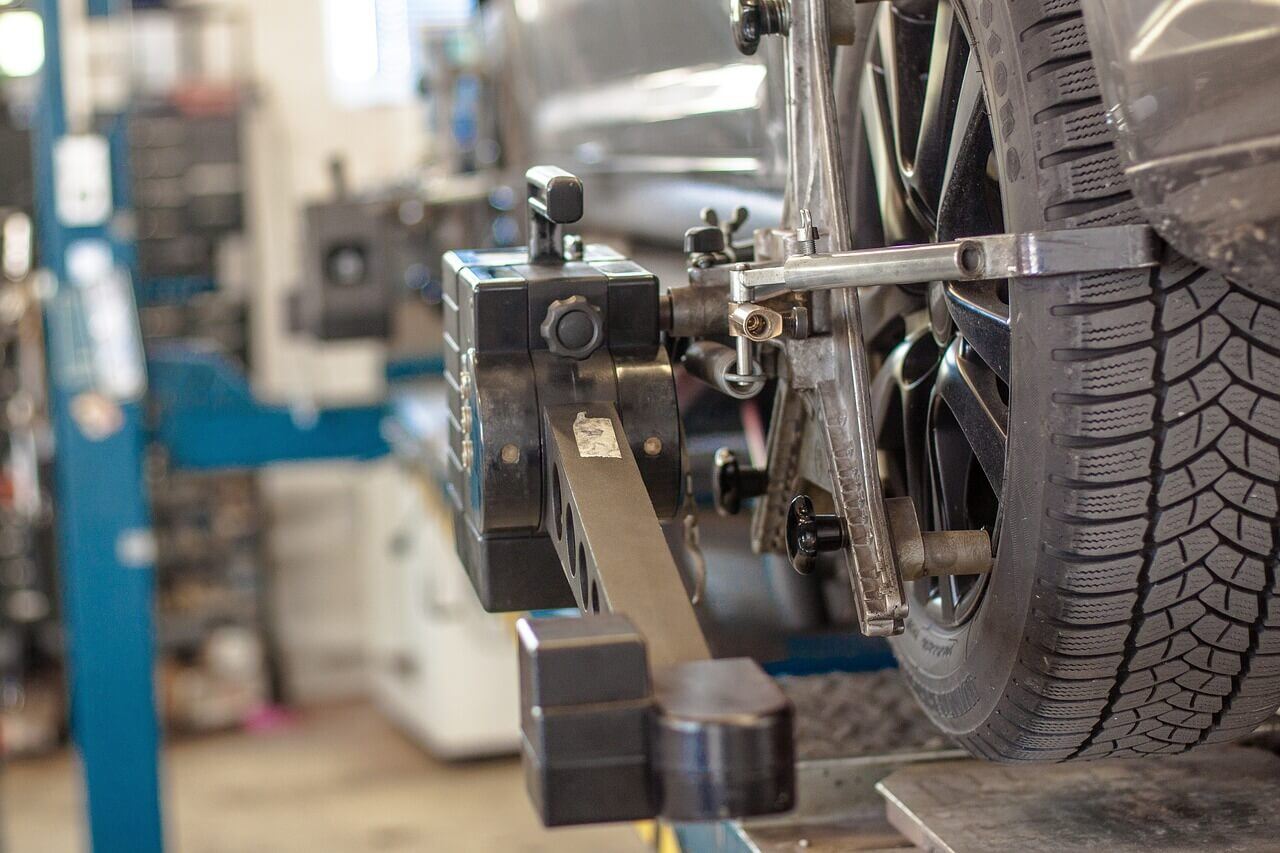
What is TISAX Assessment Level 2.5 (AL 2.5)?
by CJ Hurd on January 8, 2025 at 2:21 PM
In the realm of automotive and industrial information security, TISAX (Trusted Information Security Assessment Exchange) plays a vital role in standardizing security assessments among partners and suppliers. One of its unique features is the concept of assessment levels, which determi …
Do SOC 2 Auditors Review Your Code? Here's the Truth
by Bernard Gallagher on December 26, 2024 at 1:04 PM
For organizations pursuing SOC 2 compliance, understanding the scope and focus of the audit process is crucial. A common question that arises is whether auditors review source code as part of the SOC 2 audit. Having clarity on this topic is essential, and organizations can benefit fro …
NIST AI Risk Management Framework Explained
by Jerry Hughes on December 20, 2024 at 11:00 AM
Artificial intelligence (AI) is transforming industries, but with its rapid adoption come risks that organizations must address to ensure safe and ethical use. The NIST Artificial Intelligence Risk Management Framework (AI RMF), developed by the National Institute of Standards and Tec …
Here's Why Your Car Dealership Needs Cybersecurity
by Nicholas Foisy on December 9, 2024 at 2:10 PM
In previous blogs, we’ve explored TISAX and the cybersecurity challenges facing the automotive supply chain. However, there’s another critical area in the automotive sector increasingly targeted by cybercriminals: auto dealerships. As the backbone of vehicle sales and services, dealer …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)