WanaCry Ransomware: A Survival Guide
by George Seerden on June 7, 2017 at 10:07 AM
What is WannaCry Ransomware? WanaCrypt0r, WanaDecryt0r, and WannaCry are different names for essentially the same thing. Technically WanaCrypt0r is name of the executable, WanaDecrypt0r is the name of the decrypting utility, and WannaCry is what it makes people want to do. But, for mo …
Why Your Information Security Program Must Evolve...NOW!
by Geoff Yeagley on April 12, 2017 at 10:39 AM
Note: For the purposes of this blog post, we are going to be looking at breach data for the United States only in 2016 2016 was a record year when it comes to data breaches, according to the Identity Theft Resource Center. According to the center, there were a total of 1,093 breaches …
What is Social Engineering? Part I
by Derek Morris on March 14, 2017 at 9:45 AM
This post will be the first part in a series of three blog posts that outlines some of the most common methods “hackers” use, from a very high level, to gain access to your systems though social engineering tactics. The next two posts will dig a bit deeper into the different methods, …
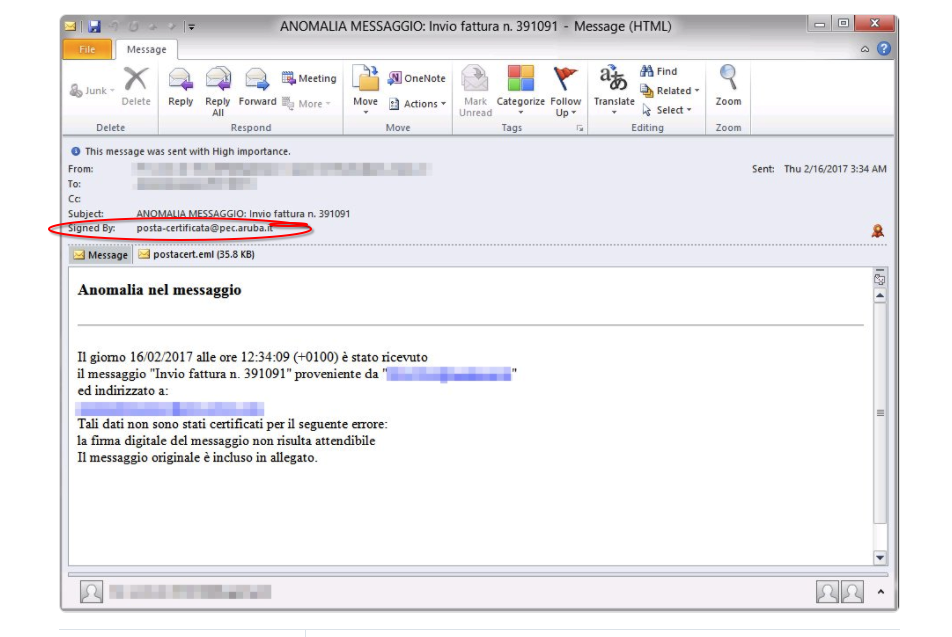
Phishing Examples - Protect Yourself From Ransomware
by Geoff Yeagley on March 8, 2017 at 10:38 AM
Fact: Phishing is the number one strategy that bad actors use to deliver malware to your organization. Fact: Phishing attacks come in a few different forms, known as phishing attacks and spear-phishing attacks. Fact: Ransomware is the most prevalent and dangerous form of Malware out t …
Vendor Management Requirements for Financial Institutions in New York
by Geoff Yeagley on December 12, 2016 at 9:29 AM
I recently wrote a blog post that discussed legislation in the State of New York that is set to take effect on January 1, 2017. This legislation will effect all financial institutions in the state around Cybersecurity and the development of a formal Cybersecurity program. Click here t …
5 Quick Tips To Help With Information Security
by Geoff Yeagley on November 29, 2016 at 1:30 PM
Information Security is a moving target. Once you "think" that you have it figured out, boom, here comes another new threat to knock you back on your heels and question just how strong your Information Security program is. That's the bad news. The good news is that we are going to giv …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)