IT Security in the Professional Sports World
by Derek Morris on August 28, 2019 at 1:02 PM
This blog will be the first in a multi-part informational blog series on professional sport team’s information technology (IT) security hurdles and the very public issues that have occurred.
FINRA 2019 Priorities Letter Released
by CJ Hurd on January 30, 2019 at 10:54 AM
In this blog we’ll be discussing the release of the Financial Industry Regulatory Authority’s (FINRA) 2019 Risk Monitoring and Examination Priorities Letter. The letter, released on January 22nd, 2019, highlights new priorities and identifies ongoing areas of concern for the coming ye …
Why a Risk Assessment is the Beginning of Security, Not the End!
by Derek Boczenowski on April 10, 2018 at 9:30 AM
In the past several weeks, the news has been filled with multiple compromises and hacks. Panera Bread, Delta, and Under Armor just to name a few. One of the ones that has had the most impact is the ransomware attack on the City of Atlanta.
IT GRC - Let's Talk About Risk!
by Geoff Yeagley on July 28, 2016 at 10:18 AM
Earlier this week we discussed IT Governance, Risk, and Compliance (IT GRC) with a specific focus on IT Governance. To read more of that post, click here. Today we are going to focus on the second component of IT GRC, IT Risk. In keeping with consistency, Gartner defines IT Risk as "t …
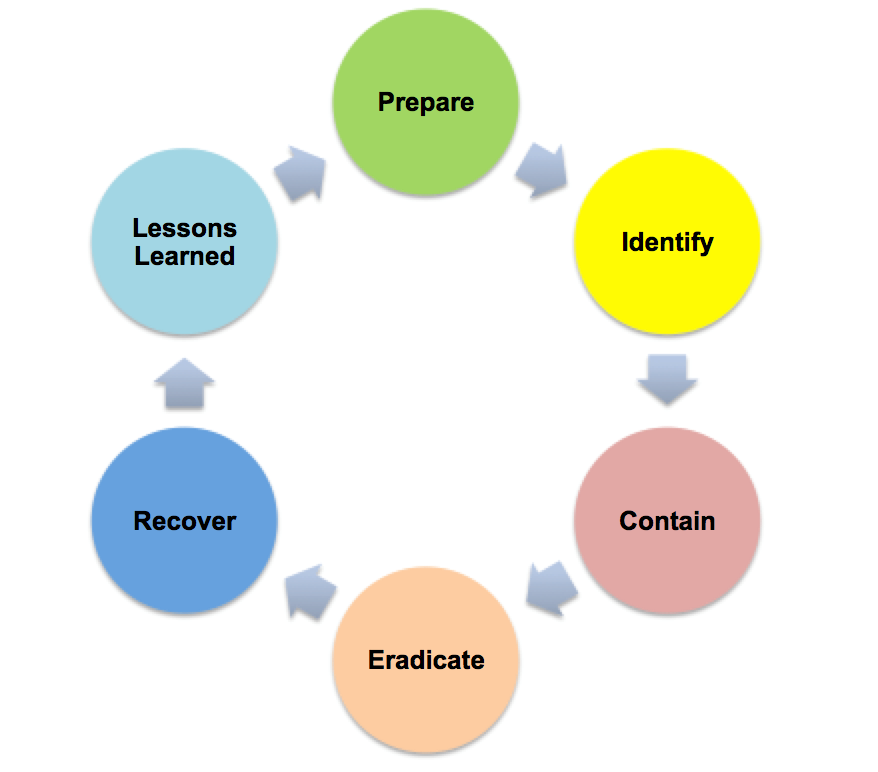
Critical Security Control 19: The Incident Response Plan
by Geoff Yeagley on May 17, 2016 at 12:16 PM
In the world of Information Security, we have all heard of the Center for Internet Security Top 20 Critical Security Controls (CSC's) which is formerly known as the SANS Top 20. This is a list of the 20 IT Security Controls that an organization can implement to strengthen their IT Sec …
The HIPAA Risk Assessment - Who Needs One and When?
by Geoff Yeagley on March 9, 2016 at 10:30 AM
Healthcare breaches are nothing new, in fact they have become quite common in the news on a weekly basis. As an example of this, a Central Florida Oncology provider recently announced that it suffered a data breach at the hands of a hacker, resulting in the compromise of the personal …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)